Immediate CRUD endpoint coverage
Query and mutate source data through runtime endpoints per table without waiting for custom backend scaffolding.
Feature
Expose source-level CRUD endpoints instantly and secure runtime access with scoped API keys so frontend teams can ship live integrations earlier.
Query and mutate source data through runtime endpoints per table without waiting for custom backend scaffolding.
Authenticate runtime requests with source-level keys to keep integrations isolated and easier to manage across environments.
Start integrating real request flows while core backend systems are still evolving, reducing idle time and rework.
Frontend teams often lose momentum when API contracts are delayed or unstable. Runtime API access solves this by exposing live CRUD endpoints from your configured source, allowing teams to wire real interactions instead of relying on static mocks.
This makes validation more meaningful because user journeys can be tested against realistic request and response behavior from the start.
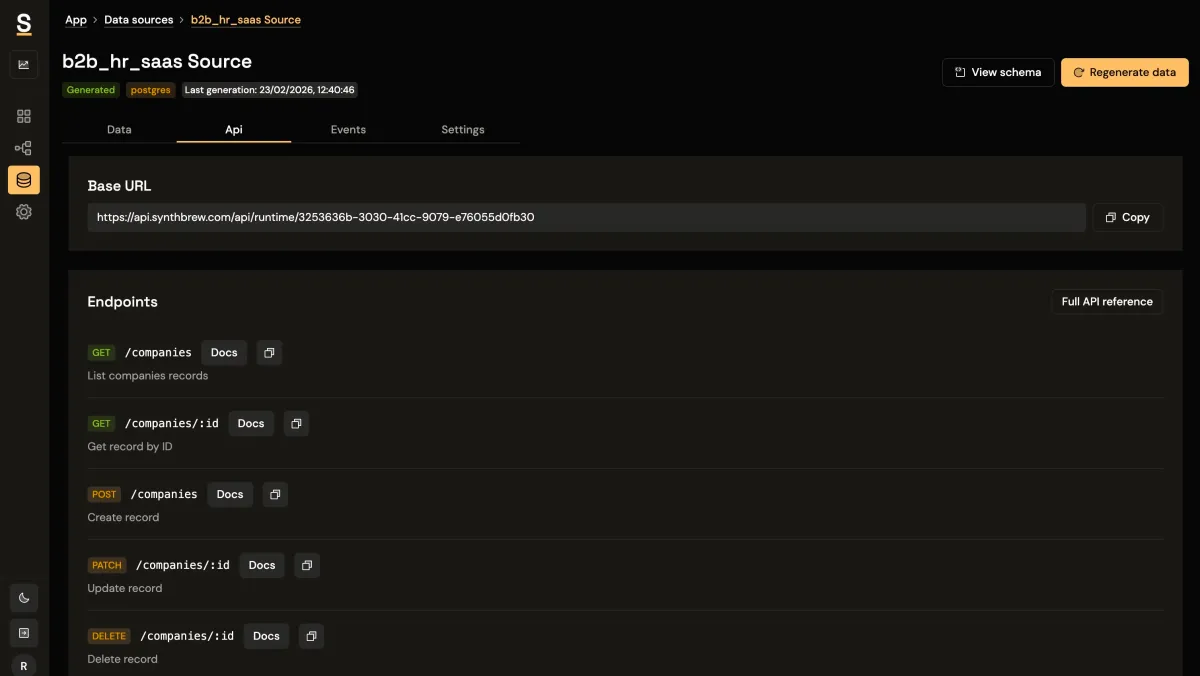
Runtime calls are secured through source-level API keys, which keeps access boundaries explicit and practical. Teams can issue keys per source, rotate them when required, and avoid sharing broad credentials across unrelated environments.
This approach supports safer collaboration, especially when multiple teams or clients consume different source datasets.
When live endpoints are available early, product development no longer has to wait for full backend completion before validating critical flows. Designers, frontend engineers, and QA can test real interactions, then hand off better-defined requirements for long-term backend implementation.
That shortens the path from prototype behavior to production-ready integration because fewer assumptions survive into later stages.
Teams that integrate early with authenticated runtime endpoints catch contract issues sooner, surface edge cases before launch windows, and reduce the gap between demo behavior and shipped behavior. The result is a more predictable release process with less late-stage integration risk.
For complete capability context, review the full features overview and compare deployment limits on pricing.
Use this playbook as your starting point, then compare other solution tracks or plan limits for your rollout.